ISJ Exclusive: Mobile technology is here to stay

James Thorpe
Share this content
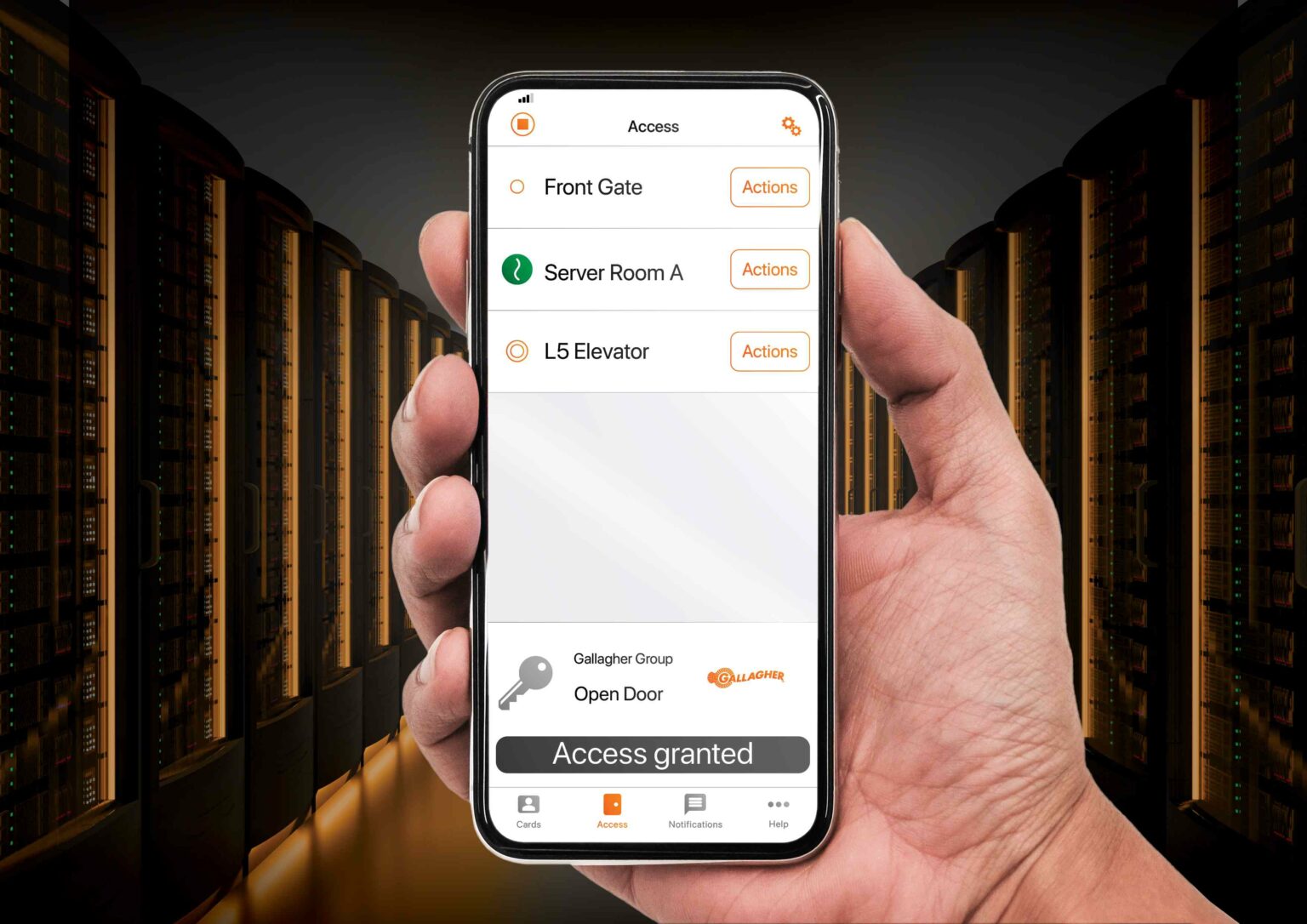
Steve Natton, Strategic Business Development Manager, Gallagher Security UK looks at five reasons to integrate mobile technology into your security solution.
Mobile technology use in everyday life has increased in recent years. Most of us have a mobile device that we use to manage different aspects of our lives – from banking, to accessing public transport, and even paying for a coffee. With approximately half of all web traffic around the globe coming from mobile device users, the move to mobile is having a major impact on industries worldwide.
In addition to security benefits, utilising mobile technology as part of a solution offers many benefits to organisations. When implemented as part of one integrated system, mobile credentials are easy to deploy, simple to operate and provide administration efficiencies and cost saving opportunities.
Ease of deployment
Ease of deployment is an advantage that’s particularly important in situations where security systems need to be installed quickly and efficiently. With mobile technology, security systems can be deployed and managed without the need for complex wiring and infrastructure.
One of the main benefits of mobile-based security systems is that they can be easily installed and managed remotely. This feature can be especially useful for companies with multiple locations or for businesses that require constant monitoring of their assets. Additionally, mobile-based security systems require less maintenance than traditional systems, which means that they can be left in place for longer periods without the need for frequent repairs or maintenance.
Another advantage of mobile technology is its scalability, which allows security systems to be easily scaled up or down as needed. Ease of deployment is also a crucial factor to consider when selecting a security system. Mobile-based security systems can be easily installed, managed remotely and require less maintenance, making them a very practical option.
Safety
Mobile technology can play a vital role in ensuring compliance with health and safety requirements during security emergencies. In an evacuation scenario, mobile technology can be used to verify the safety of cardholders, reducing the time spent on mustering. Mobile technology allows wardens to operate and monitor the evacuation process remotely, ensuring full visibility of movement on-site and enabling them to move people to safe zones while keeping track of those who have not reported to the evacuation zone.
Similarly, mobile technology can improve the lockdown process by facilitating faster initiation and effective communication. In the event of a lockdown, mobile security solutions can ensure a fast lockdown process while providing people on site with the information they need to keep themselves safe. Notifications sent to staff/student devices can be more effective than emails or SMS messages as they receive higher engagement and are a more affordable option for mass communication.
Efficiency
Mobile technology removes the need for the operator and cardholder to be present in the same place at the same time to provision and receive credentials. This allows the operator to provision mobile credentials at a time that suits them and allows for instant access when the cardholder arrives on site. At universities, in particular, this can save huge administrative efforts at the beginning of a semester, when large numbers of students are arriving on campus at the same time and require access into lecture theatres and halls of residence.
Integrating mobile technology into a security system can improve the efficiency of security operations in several ways. Firstly, mobile technology can enable personnel to remotely access and monitor systems, allowing for faster response times. This can help to identify potential security threats and resolve them quickly, preventing incidents from escalating.
Secondly, mobile technology can provide security personnel with access to critical information, such as floor plans, evacuation procedure, and emergency contact details. This information can be easily accessed from mobile devices. Thirdly, mobile technology can help to automate processes, such as monitoring access to restricted areas, generating reports and tracking incidents. This can reduce the workload on security personnel and free up time for more critical tasks.
Fourthly, mobile technology can enable faster communication and collaboration between security personnel, allowing them to share information and coordinate their response to security incidents more effectively. This can help to improve the overall efficiency of operations and reduce the time required to resolve security incidents. Lastly, mobile technology can provide security personnel with more flexibility, enabling them to work remotely and access security systems from any location.
Cost savings
In addition to time, mobile credentials can also save organisations money. Mobile credentials are more affordable than access cards when compared to the costs of purchasing, printing and distributing the cards; by utilising technology that is already in possession of users, organisations can reduce plastic waste and emissions associated with creating and shipping access cards throughout the organisation.
Integrating mobile technology into a security system can also help achieve cost savings by reducing the costs associated with physical security infrastructure such as cameras, alarms and monitoring systems. Mobile devices can be used to provide remote surveillance and monitoring, eliminating the need for on-site security personnel and enabling businesses to save on associated costs such as salaries and benefits.
Mobile technology can also reduce maintenance costs and improve system reliability. Traditional security systems require regular maintenance and repairs, which can be expensive and time consuming. Mobile-based security systems, on the other hand, require less maintenance and are less susceptible to failures due to the absence of complex wiring and infrastructure.
Security processes can be streamlined using mobile technology and time spent on manual tasks, such as generating reports or accounting for everyone’s safety during evacuations, can also be reduced. With mobile-based security systems, these tasks can be automated, reducing the workload on security personnel and freeing up time for other tasks.
Remote management
Mobile security solutions allow operators to manage day-to-day issues remotely. Tasks such as unlocking doors, managing alarms and disabling cardholders in the event of a lost credential, can be easily managed on the go via a secure mobile app that communicates directly with the security software. By freeing security operators from the control room, they can easily respond to security events from anywhere on site, as and when they arise.
What does the future hold?
As technology progresses and the world becomes more mobile, it’s inevitable mobile technology will become more prevalent in the security industry. While it is difficult to predict exactly what the next big development will be, it could be anticipated that digital IDs will become a feature of mobile security in the near future.
In utilising a secure digital ID that can be displayed on a mobile device, organisations can navigate one of the barriers to mobile security – the need for staff to carry a separate ID card in addition to their mobile access credential.
The emergence of IoT and smart technology is accelerating our desire, as consumers, to integrate mobile technology into our everyday lives. From million-dollar smart city projects to the ability to switch on your washing machine from your mobile phone, we all want to be a part of the technology evolution. With the associated cost efficiencies and environmental benefits, mobile has established an influential role in our future – not only for the security industry, but all aspects of our lives.
In this ever-changing world, it is now more important than ever for businesses to review their security strategy and consider the extensive efficiency and safety benefits that mobile provides.
To learn more about Gallagher’s mobile credential technology, visit: https://security.gallagher.com/Solutions/Mobile-Solutions
This article was originally published in the May edition of ISJ. To read your FREE digital edition, click here.



